Automated Threat Classification using Machine Learning
 IsMalicious Team
IsMalicious Team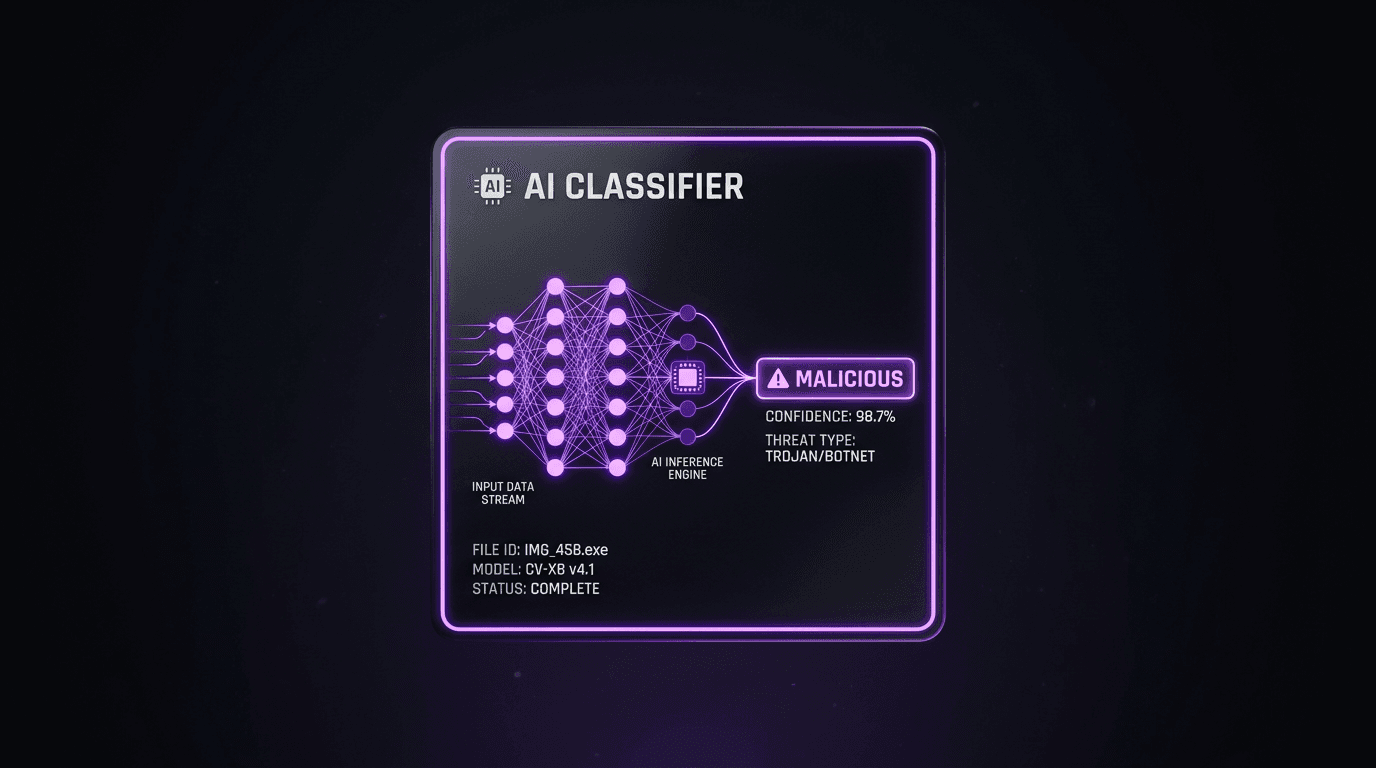
The speed and volume of modern cyber attacks have surpassed human capacity for manual classification. Machine Learning (ML) offers a solution, enabling automated, real-time threat classification at scale.
The Challenge of Manual Classification
Manual analysis is:
- Slow: It takes time to investigate headers, payloads, and behavior.
- Inconsistent: Different analysts may classify the same incident differently.
- Unscalable: You cannot hire enough analysts to review every alert.
How ML Helps
Machine Learning models can be trained on massive datasets of known malicious and benign traffic to identify patterns that humans might miss.
Key Applications
- Phishing Detection: NLP (Natural Language Processing) models analyze email body text and subject lines to detect semantic anomalies indicative of social engineering.
- Malware Classification: Models analyze file characteristics (static analysis) and execution behavior (dynamic analysis) to classify malware families (e.g., Emotet vs. Trickbot).
- DGA Detection: ML algorithms can spot Domain Generation Algorithms (DGAs) used by botnets by analyzing the randomness of domain names.
The Human-in-the-Loop
While ML is powerful, it is not perfect. The most effective systems use a Human-in-the-Loop (HITL) approach:
- High Confidence: AI automatically blocks and classifies.
- Low Confidence: AI flags for human review.
- Feedback Loop: Human decisions are fed back into the model to improve future accuracy.
Conclusion
Automated threat classification using ML is essential for reducing Mean Time to Respond (MTTR). By offloading the heavy lifting of categorization to AI, human analysts are freed to focus on complex investigations and strategic defense.
Related articles
 Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World DefensesExplore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
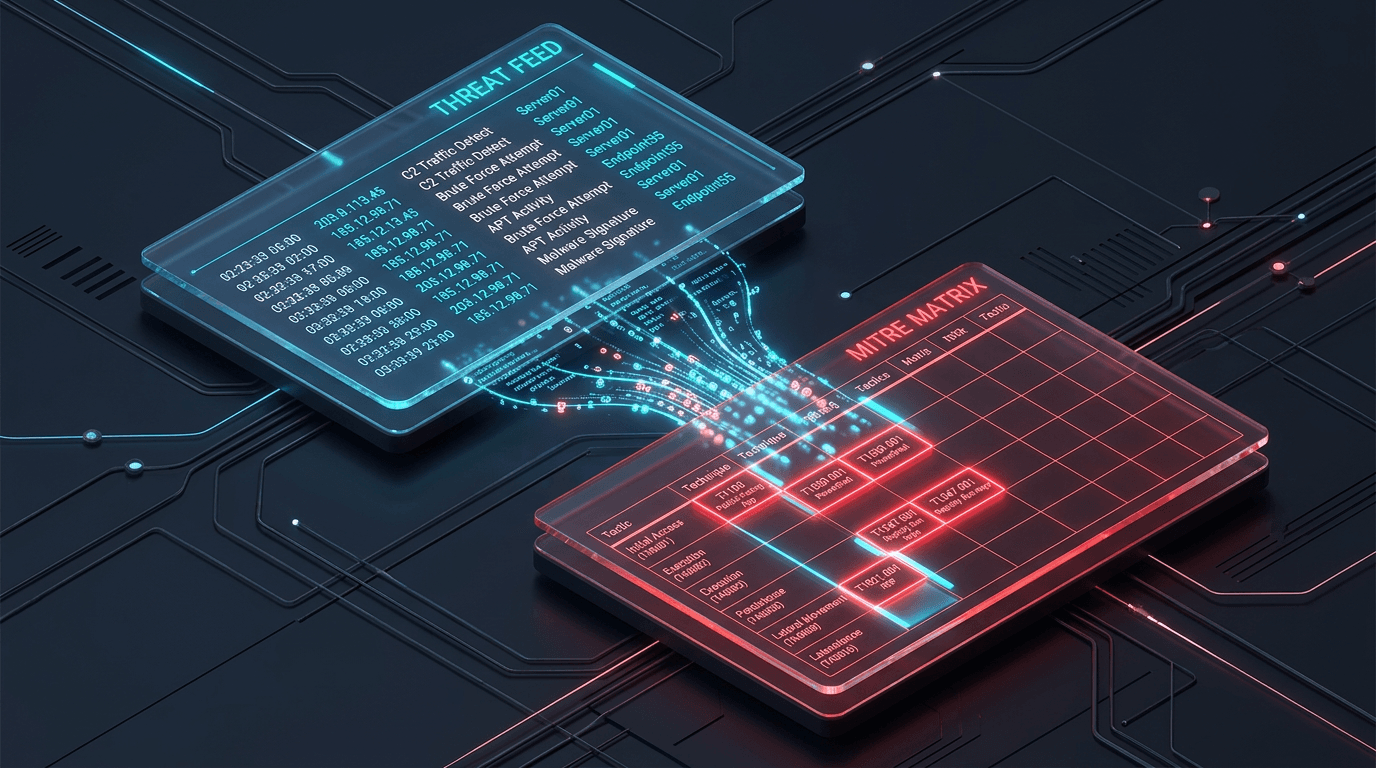 Mar 17, 2026Integrating MITRE ATT&CK with Real-Time Threat Feeds
Mar 17, 2026Integrating MITRE ATT&CK with Real-Time Threat FeedsBridge the gap between strategic frameworks and tactical defense. Learn how to map real-time threat feeds directly to the MITRE ATT&CK matrix.
 Jan 2, 2026AI-Powered Cyberattacks: How Threat Actors Use Machine Learning
Jan 2, 2026AI-Powered Cyberattacks: How Threat Actors Use Machine LearningCybercriminals are weaponizing artificial intelligence to launch sophisticated attacks at unprecedented scale. Learn how AI-powered threats work and how threat intelligence can help you defend against them.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker