The Rise of API Attacks: Protecting the Modern Attack Surface
 IsMalicious Team
IsMalicious Team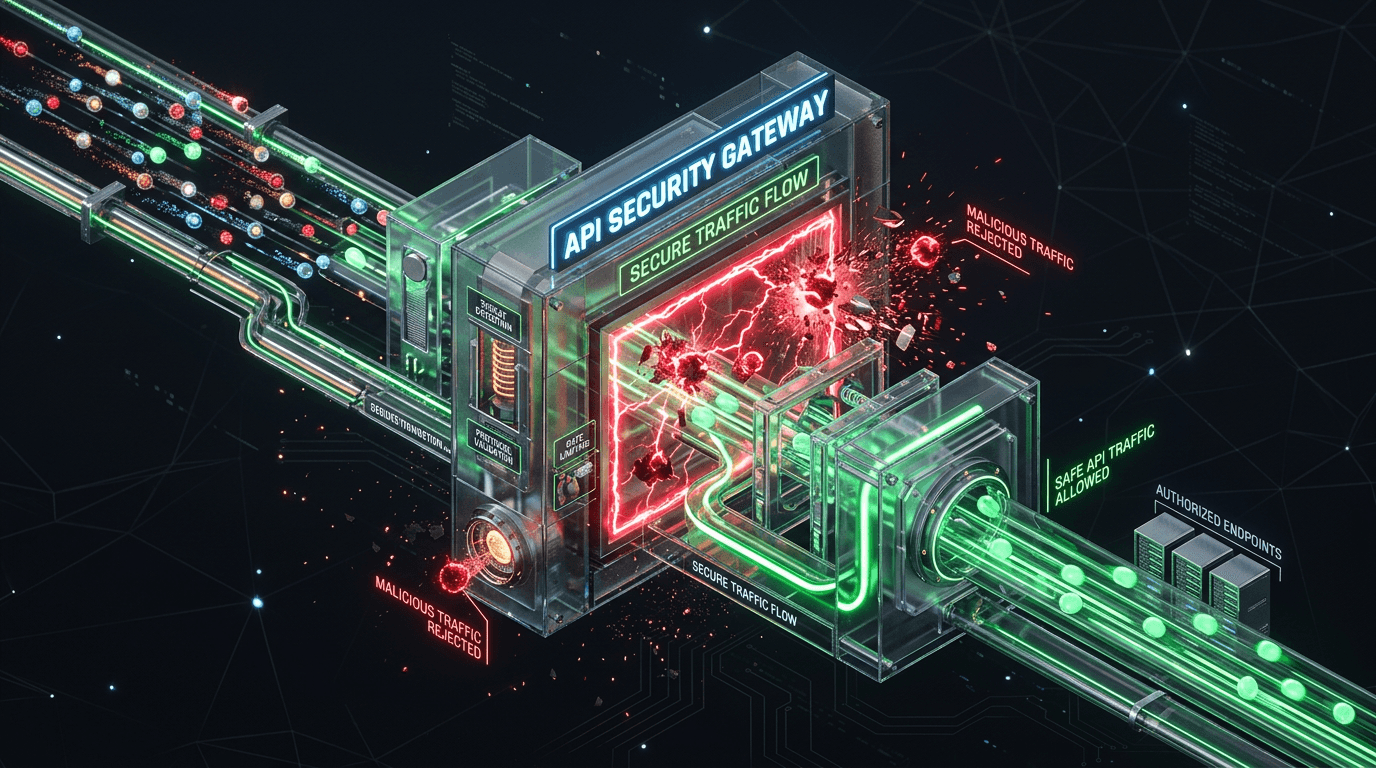
As organizations rush to digitally transform, Application Programming Interfaces (APIs) have become the backbone of modern software. They connect mobile apps to backends, microservices to each other, and businesses to partners.
However, this ubiquity has made APIs a prime target for attackers.
Why APIs are Vulnerable
Unlike traditional web applications, APIs often expose the underlying logic and data structure of an application.
- Over-Permissioning: APIs frequently return more data than the client needs, relying on the client to filter it (Mass Assignment).
- Broken Authentication: Many APIs lack robust authentication mechanisms, especially for machine-to-machine communication.
- Rate Limiting Gaps: Without proper throttling, APIs are susceptible to Denial of Service (DoS) and brute-force attacks.
The OWASP API Security Top 10
The Open Web Application Security Project (OWASP) maintains a specific list for API vulnerabilities. Key threats include:
- Broken Object Level Authorization (BOLA): An attacker can manipulate the ID of an object (e.g.,
user_id=123) to access another user's data. - Broken User Authentication: Weaknesses in session management or credential handling.
- Excessive Data Exposure: Returning full object properties instead of a specific subset.
Securing Your APIs
- Inventory Everything: You cannot protect what you don't know exists. Maintain an up-to-date catalog of all APIs (Shadow APIs are a major risk).
- Implement Strong Auth: Use standards like OAuth 2.0 and OpenID Connect.
- Validate Input: Treat all data from API requests as untrusted.
- Rate Limit & Throttle: Prevent abuse by limiting the number of requests a client can make.
- Use an API Gateway: Centralize security policies, monitoring, and enforcement.
Conclusion
API security requires a shift in mindset. It's not just about protecting the perimeter; it's about securing the data flow itself. By understanding the unique risks of APIs, developers and security teams can build more resilient applications.
Related articles
 Feb 10, 2026Best Threat Intelligence APIs Compared (2026): The Complete Guide
Feb 10, 2026Best Threat Intelligence APIs Compared (2026): The Complete GuideA comprehensive comparison of the top threat intelligence APIs in 2026 — isMalicious, VirusTotal, AbuseIPDB, AlienVault OTX, Shodan, and URLhaus. Feature matrices, pricing breakdowns, and recommendations by use case.
 Feb 7, 2026API Security Best Practices: Defending Against the OWASP Top 10
Feb 7, 2026API Security Best Practices: Defending Against the OWASP Top 10APIs are the backbone of modern applications but are often left vulnerable. Learn how to secure your APIs against common attacks like broken object level authorization and injection.
 Apr 26, 2026IOC Enrichment APIs: A Security Operations Guide to Faster Triage, Fewer False Positives, and Measurable ROI
Apr 26, 2026IOC Enrichment APIs: A Security Operations Guide to Faster Triage, Fewer False Positives, and Measurable ROIAn indicator without context is a ticket without an owner. Learn how IOC enrichment APIs work, which fields SOC teams need at each tier, and how to wire them into case management without building a data swamp.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker