The Evolution of Threat Intelligence in 2026
 IsMalicious Team
IsMalicious Team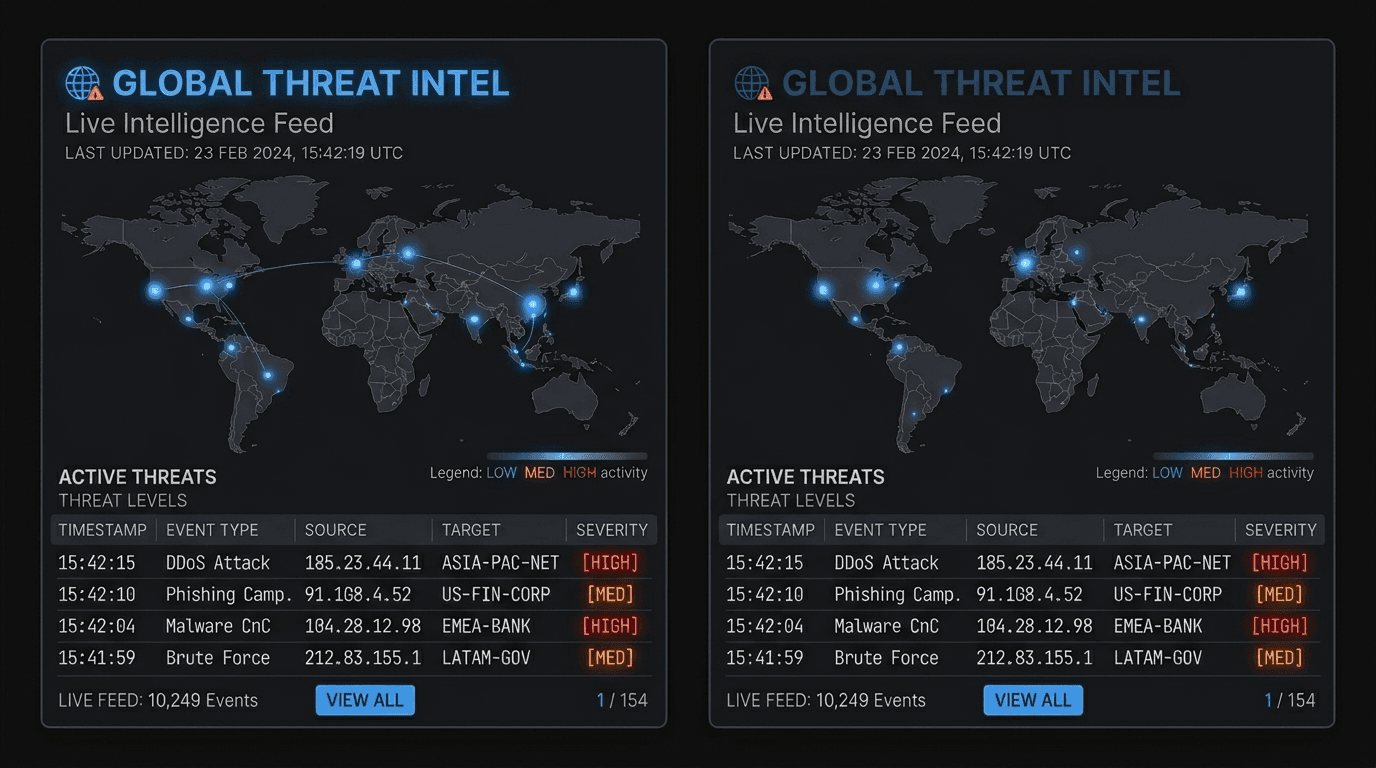
In 2026, Threat Intelligence (TI) is no longer a luxury for elite security teams; it is a fundamental component of every effective cyber defense strategy. But the nature of TI has changed dramatically over the last few years.
From Data to Wisdom
Historically, threat intelligence was often synonymous with "feeds"—massive lists of bad IP addresses and domains. While useful, this raw data often lacked context. Today, the focus has shifted from information to intelligence.
- Context is King: Knowing that an IP is bad is not enough. You need to know why it's bad, who is using it, and what they are targeting.
- Strategic Intelligence: TI is now informing business decisions, not just firewall rules. Boards want to know about geopolitical risks and industry-specific trends.
The Role of Automation
With the sheer volume of threats, manual analysis is impossible.
- Automated Ingestion: SOAR platforms automatically ingest TI feeds and update security controls in real-time.
- Generative AI: AI models are now summarizing complex threat reports and even predicting potential attack vectors based on historical data.
Integration is Key
Threat intelligence does not exist in a vacuum. It must be woven into the fabric of your security stack.
- SIEM Enrichment: Correlating internal logs with external threat data to spot hidden attacks.
- Vulnerability Management: Prioritizing patching based on which vulnerabilities are actually being exploited in the wild (CISA KEV).
Conclusion
The future of threat intelligence is integrated, automated, and highly contextual. Organizations that leverage modern TI effectively will be able to anticipate attacks rather than just reacting to them.
Related articles
 May 1, 2026SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams Sane
May 1, 2026SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams SaneA SOAR playbook without enrichment is a ticket printer. A SIEM with unbounded threat feeds is a bill. Here is a practical way to design enrichment for Splunk, Sentinel, or Elastic-style stacks—what to store, when to run playbooks, and what to report upward.
 Apr 26, 2026Building IOC Pipelines: From Raw Indicators to Operational Threat Intelligence in 2026
Apr 26, 2026Building IOC Pipelines: From Raw Indicators to Operational Threat Intelligence in 2026A practical engineering guide to building indicator of compromise (IOC) pipelines—ingestion, normalization, deduplication, enrichment, scoring, distribution, and feedback—to turn raw threat feeds into operational defense.
 Apr 19, 2026Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026
Apr 19, 2026Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026A complete guide to the three levels of threat intelligence—strategic, operational, and tactical—with practical examples of consumers, outputs, feeds, and how to connect them into a coherent CTI program.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker